Content types
Categories
- Accounting & Finance
- Alternative Investments
- Career Guidance
- Change & Transformation
- Creating Exceptional Experiences
- Cyber Security
- Disruptive Technology
- Enterprise Technology
- Finance Transformation
- Human Resources
- Leadership
- Life at Stanton House
- Stanton House News
- Strategy & General Management
- Technology
- The Hiring Process

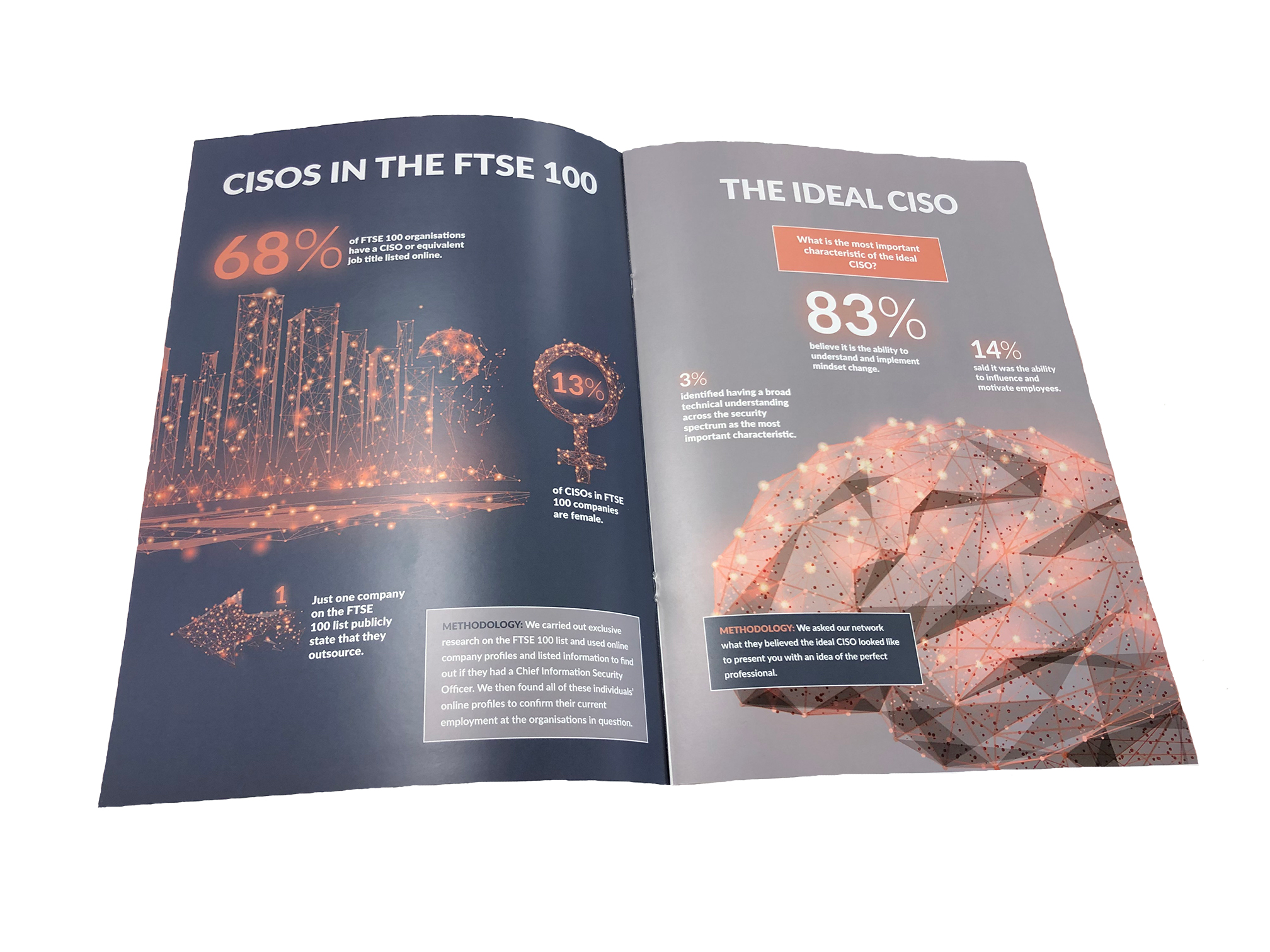
Insight papers
We take great pride in being able to share expert knowledge and having an opinion on the topics that will impact your hiring success or professional career.
Explore and download our recent insight papers.